Modern companies rely on secure remote access, cloud systems, and distributed workforces, making virtual private networks a business necessity rather than a luxury. An enterprise vpn provider offers the infrastructure to encrypt traffic, authenticate users, and centralize network control. With rising cyber threats, organizations must ensure that every user connection remains protected, whether employees log in from the office, airport, or another continent. Enterprise VPN solutions offer centralized policy management, reporting features, and compliance readiness that consumer VPNs lack. They help companies scale securely, enforce least-privilege access, and meet regulatory standards. In this blog, we explore industry-leading enterprise VPNs and highlight the features that make them suitable for growing businesses. These tools vary in architecture and deployment design, giving organizations multiple paths to implement a secure foundation for long-term digital success.
Quick Comparison Table: Enterprise VPN Provider- at a Glance
| Feature | Enterprise VPN | Consumer VPN |
|---|---|---|
| Admin Control | Yes | No |
| User Management | Yes | No |
| Zero Trust | Yes | Rare |
| Compliance Tools | Yes | No |
| Logging & Reports | Yes | Limited |
Key Benefits of Using an Enterprise VPN Provider
- Encrypts business traffic to keep sensitive data secure
- Supports remote and hybrid teams with safe network access
- Centralizes authentication for better identity control
- Helps organizations meet regulatory and compliance standards
- Provides monitoring tools for tracking user activity and threats
- Reduces risks tied to unsecured networks and public Wi-Fi
List of the Best Enterprise VPN Providers
Below are the top enterprise VPN solutions trusted by businesses worldwide.
Cisco AnyConnect Secure Mobility VPN
Best For: Large Enterprises & Global Teams
Cisco AnyConnect has long been one of the most commonly deployed corporate VPNs due to Cisco’s strong security presence in enterprise networking. The solution provides encrypted tunnels, device posture assessment, and strong user authentication. Businesses benefit from reporting dashboards that help IT teams review connection histories, detect anomalies, and identify policy violations in real time.
Cisco AnyConnect supports laptops, virtual desktops, and mobile platforms, ensuring consistent security across all employee devices. The VPN also integrates into Cisco’s broader security ecosystem, including firewalls, identity platforms, and secure web gateways. Organizations that require high reliability can also take advantage of Cisco’s global infrastructure and proven enterprise stability. As an enterprise vpn provider, Cisco continues to support large-scale deployments for governments, Fortune 500 companies, and global service providers, making it a trusted name in secure network access.
Palo Alto Prisma Access
Best For: Cloud-First Companies
Palo Alto’s Prisma Access takes a cloud-first approach to secure remote access. Instead of routing users to a centralized VPN hub, Prisma Access pushes security controls into the cloud, improving performance while reducing bottlenecks. This approach allows users to connect to the nearest available access point, resulting in improved latency and a smoother application experience.
Prisma Access also provides built-in threat prevention, URL filtering, and user behavior monitoring to detect unusual activity instantly. Companies can combine remote access with Palo Alto’s firewall and Zero Trust components to create a unified security umbrella for multiple offices and remote teams. With centralized management, updates become seamless and configuration remains consistent across the organization. This platform appeals to fast-scaling businesses that want to eliminate hardware maintenance and leverage a distributed global network for secure connectivity.
NordLayer Business VPN
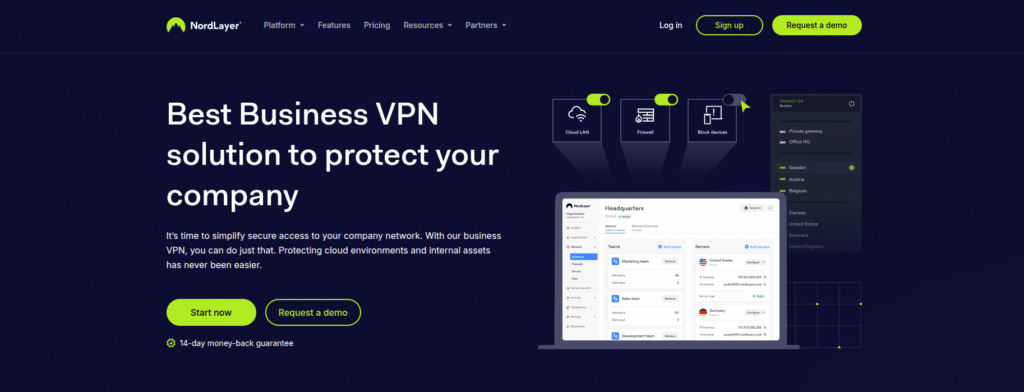
Best For: Fast Deployment & Growing Teams
NordLayer is designed for organizations seeking modern, scalable VPN deployment without heavy infrastructure requirements. The platform provides intuitive user controls, group-based access restrictions, and multi-factor authentication to strengthen identity security. Administrators can use a clean dashboard to assign access to specific resources, enforce network rules, and track activity.
NordLayer also integrates with monitoring tools, single sign-on services, and cloud environments, making it suitable for hybrid workforces. The VPN offers dedicated gateways that allow organizations to assign static IPs for logging and compliance. Pricing remains flexible, enabling smaller companies to start with limited licenses and expand as their workforce grows. NordLayer suits firms looking for an enterprise vpn provider style solution in a lightweight, cloud-managed package while still delivering enterprise-class encryption and performance. Its clean interface also makes administration simpler for IT teams without large network engineering staff.
Zscaler Zero Trust Exchange
Best For: Zero Trust Access Models
Zscaler transforms traditional VPN access by replacing network-wide connectivity with identity-based access to specific applications. Instead of granting users entry into the entire network, Zscaler verifies device posture and identity before granting access only to approved services. This structure eliminates east-west lateral movement, which has historically been a major attack vector.
Zscaler operates entirely in the cloud and manages encrypted traffic inspection, activity logging, threat filtering, and out-of-band policy enforcement. Companies benefit by offloading hardware maintenance and simplifying security policies. The platform also integrates with major identity providers, including Okta and Azure AD, to streamline authentication. For organizations modernizing security architectures, Zscaler provides a cloud-native alternative to legacy VPN systems while still serving the needs of companies exploring a reliable enterprise security strategy.
Fortinet FortiGate
Best For: High-Performance Networks
Fortinet FortiGate combines firewall technology with high-performance VPN encryption capabilities in a single product line. IT administrators can deploy FortiGate appliances in offices, data centers, or cloud environments, giving organizations architectural flexibility. Fortinet supports strong identity controls, intrusion prevention, and advanced threat analysis with machine-learning-driven intelligence. Companies can manage configurations through Fortinet’s centralized management console, which provides detailed traffic analytics and event monitoring.
As an enterprise vpn provider, Fortinet helps large enterprises maintain stable VPN performance while enjoying a tightly integrated network security stack. FortiGate is especially popular among companies that want to manage firewalls and encrypted access through a single vendor, simplifying procurement, support, and licensing. Its scalability and hardware acceleration make it an excellent fit for bandwidth-heavy environments such as global offices or large manufacturing sites.
Perimeter 81 Zero-Trust VPN
Best For: Startups & Mid-Sized Businesses
Perimeter 81 focuses heavily on usability and modern remote workforce support. The platform provides automated network provisioning, device posture checks, and cloud-native gateways that eliminate the need for on-premises hardware. Administrators can segment resources into isolated network regions and grant users role-based access. This reduces the risk of unauthorized network movement while improving internal visibility.
Perimeter 81 serves as an excellent choice for startups and mid-sized companies that want the flexibility of a secure enterprise vpn provider style solution without complex deployment. It also supports integrations with common SaaS products and identity tools, making it easier to implement in hybrid environments. The interface simplifies onboarding, reducing the time required to secure remote workers. This makes Perimeter 81 a practical VPN option for fast-growing organizations with limited hands-on security engineering resources.
Check Point Harmony Connect
Best For: Companies Using Check Point Ecosystem
Check Point Harmony Connect provides a cloud-delivered approach to remote access, offering encrypted tunnels along with threat detection, secure web browsing, and application-level controls. Security updates propagate across the network automatically, ensuring users receive current signatures without local maintenance. The platform integrates well with Check Point’s broader security suite, offering administrators unified dashboards and consistent reporting.
Harmony Connect also supports identity-based rules and integrates with major authentication systems. As an enterprise vpn provider, Check Point gives organizations a strong balance between legacy security capabilities and modern cloud delivery. Companies benefit from reduced hardware maintenance costs, simplified connection management, and improved threat response times. The platform works well for businesses standardizing on the Check Point ecosystem and seeking a long-term, centralized security model with broad threat visibility and scalable performance across distributed office locations.
Sophos VPN and Secure Access
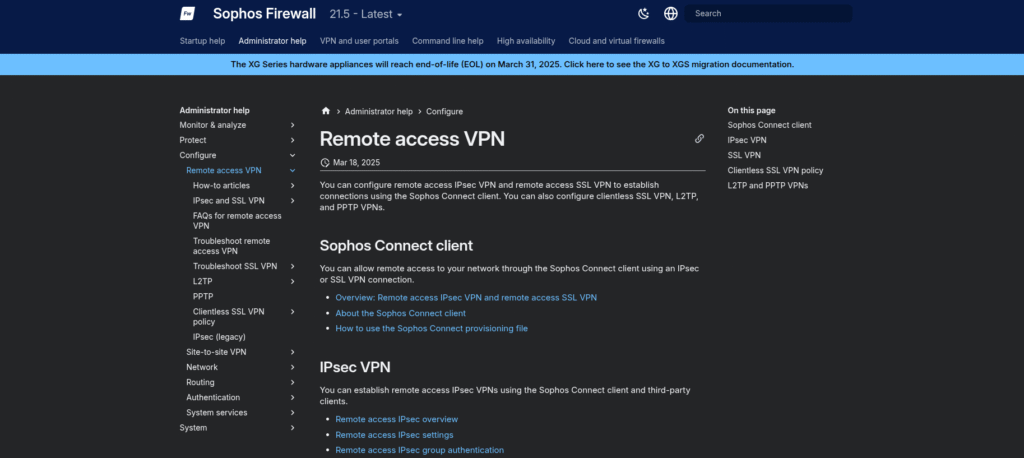
Best For: Unified Endpoint + Network Security
Sophos offers VPN functionality integrated into its firewall and endpoint protection suites, creating a layered security environment for remote workers. Administrators can configure SSL or IPSec tunnels based on business requirements, and users authenticate through credentials governed by central identity management. Sophos includes security alerts, traffic logs, and reporting dashboards to help IT departments track access patterns and unusual activity.
The VPN works seamlessly with Sophos endpoint tools, which perform malware detection, exploit protection, and device-level monitoring. This makes it easier for organizations to adopt a unified approach to remote access and desktop protection. Sophos appeals to companies that want a straightforward deployment without investing in multiple security vendors. The solution is particularly effective for mid-sized businesses needing reliable remote access supported by strong on-device security capabilities with centralized management and consistent policy enforcement.
Barracuda CloudGen Firewall VPN
Best For: Distributed Branch Networks
Barracuda CloudGen provides a performance-focused VPN environment with capabilities designed for distributed branch networks. The platform uses WAN optimization features to reduce latency and improve throughput over long-distance connections. CloudGen also incorporates application-aware routing, allowing the system to detect traffic types and prioritize them intelligently. Administrators can configure IPSec or SSL tunnels and manage policy rules from a single intuitive interface.
Barracuda integrates automated failover and traffic load balancing to maintain stable VPN availability even during outages. Reporting features give security teams the ability to analyze traffic flows, detect anomalies, and meet audit requirements. Companies that manage multiple remote offices, retail stores, or manufacturing locations will appreciate the consistency CloudGen provides across wide-area networks. Barracuda delivers enterprise-grade VPN performance with a practical set of tools that reduce network overhead and simplify long-term maintenance.
OpenVPN Access Server for Business
Best For: Customizable & Budget-Friendly Deployments
OpenVPN Access Server provides a flexible and open-standard VPN solution that appeals to companies wanting control, transparency, and the ability to customize configuration. IT teams can deploy the server on-premises or in cloud environments, including AWS, Azure, and Google Cloud. OpenVPN also provides a clean administrative dashboard that enables secure user provisioning, device monitoring, and auditing. Businesses benefit from the platform’s strong encryption and community-validated protocol design.
OpenVPN remains cost-effective, especially for organizations that want enterprise-class remote access without large licensing commitments. While additional configuration may be required compared to fully hosted solutions, the result is a transparent VPN environment tailored to specific needs. OpenVPN suits companies that want performance and security while maintaining ownership of their infrastructure and network logic. The large community ecosystem also ensures extensive documentation and technical support options.
Conclusion
Selecting an enterprise VPN requires understanding technical needs, user patterns, compliance responsibilities, and long-term scalability. An enterprise vpn provider should not only encrypt connections but also support identity-centric access, detailed reporting, and broad platform compatibility. Some organizations benefit most from traditional hardware firewalls with built-in VPN modules, while others need cloud-native systems that eliminate data center maintenance entirely. What matters is choosing a solution aligned with internal capabilities and business goals. With the rise of remote work, companies cannot afford outdated or unmonitored VPN systems that leave critical assets exposed. The providers listed in this guide represent some of the strongest options available to organizations of all sizes. By evaluating features, cost structures, deployment models, and integration needs, companies can select the right foundation for secure digital growth and mitigate cyber risks in a rapidly evolving business landscape.


Leave a Reply